
USE CASES
Remediate Blind Spots, Shadow Access and Hygiene Gaps
What You Can't See Is Already a Risk. It Just Hasn't Been Exploited Yet.
Summary
Identity blind spots aren't the result of poor security intentions. They're a natural consequence of organizational growth: fragmented environments, decentralized IT, accelerating cloud adoption, and identity sprawl across SaaS, on-prem, and AI systems. The result is a collection of unmanaged identities, undiscovered assets, and access paths that exist entirely outside security visibility, each one a potential entry point for attackers or misuse by insiders.
Key Business Challenges

Shadow Identities and Unmanaged Access Paths
Service accounts created outside IAM governance, local accounts on unmanaged systems, shadow AI agents, and personal credentials used for corporate access, each invisible to the tools built to manage and monitor identity.

Missing MFA and Authentication Gaps
Policies require MFA. Reality is different. Users bypass SSO, applications authenticate through paths that skip MFA enforcement, and the gap between policy intent and actual enforcement is never measured.

Dormant and Orphaned Identities
Departed employees with active credentials. Decommissioned service accounts still holding valid tokens. Dormant NHIs accumulating privilege over time. Each represents attack surface that has no active owner and no active monitoring.
How AuthMind Solves These Challenges
AuthMind continuously discovers and maps all identities, managed and unmanaged, across every environment, exposing blind spots, shadow access, and hygiene gaps that policy-based tools cannot detect.
Discover Shadow Identities
and Unmonitored Access Paths.
AuthMind identifies shadow NHIs, unmanaged AI agents, local accounts, and access paths operating outside IAM governance, bringing unknown identities into a unified security view and mapping them back to their corporate owners.

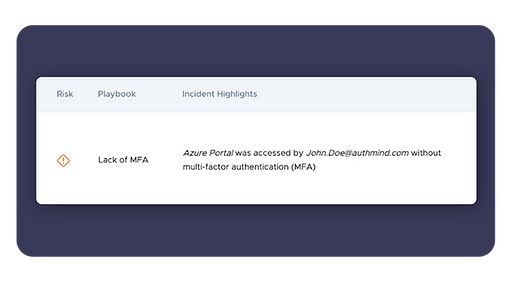
Surface MFA Gaps and Authentication Bypass.
AuthMind detects where MFA is required by policy but not enforced in practice, exposing authentication bypass paths, SSO circumvention, and applications where users authenticate outside approved identity flows.
Identify Dormant Accounts and Orphaned Identities.
Inactive accounts, expired service identities, and NHIs without active owners are surfaced automatically. AuthMind provides the context needed to prioritize remediation, distinguishing genuinely dormant identities from those still in active use.

Why it matters
You cannot remediate what you haven't discovered.
AuthMind maps the full identity landscape, including everything that falls outside your current tools, so security teams can close gaps before attackers find them.









