
USE CASES
Protect and Govern Privileged Access Bypass and MFA Weaknesses
PAM Governs What Privileged Access Is Supposed To Look Like. AuthMind Shows You What It Actually Does.
Summary
Privileged access management tools were built to control and audit access to high-value systems. What they cannot do is see around themselves. NHIs and service accounts bypass PAM entirely. Humans find paths to privileged resources that avoid the PAM workflow. MFA enforcement is declared in policy but inconsistently applied in practice. The privileged access posture most organizations believe they have is materially different from the one they actually have.
Key Business Challenges

NHIs and Service Accounts That Bypass PAM
Most NHIs and service accounts are provisioned directly, bypassing PAM controls entirely. They hold persistent credentials, accumulate privilege over time, and operate with no session recording, no audit trail, and no oversight.

Privileged Access Outside PAM Oversight
Humans access privileged resources through paths that circumvent PAM workflows, direct RDP, API keys with admin scope, or application-level access that never triggers a privileged session check. PAM sees none of it.

MFA Weaknesses in Privileged Workflows
Privileged access pathways frequently have weaker MFA enforcement than standard user flows. Step-up authentication is declared but not verified. Privileged sessions reuse tokens without re-authentication. The gaps are structural and invisible without behavioral observability.
How AuthMind Solves These Challenges
AuthMind observes privileged access behavior across all identity types, including the paths, accounts, and access flows that PAM was never built to see, delivering continuous governance assurance grounded in actual activity.
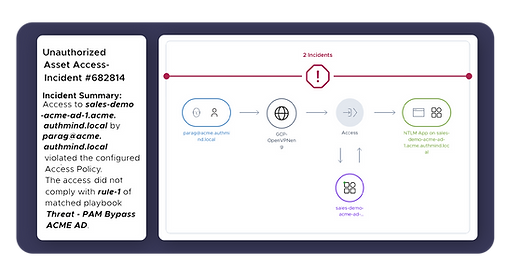
Detect Privileged Access That Bypasses PAM.
AuthMind identifies privileged access occurring outside PAM oversight, direct connections, API-level admin access, and application paths that grant elevated capability without triggering a managed session, and surfaces them for review and remediation.
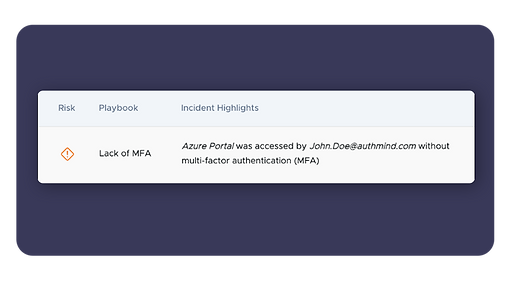
Surface MFA Weaknesses in Privileged Workflows.
AuthMind compares privileged access activity against MFA policy expectations, exposing step-up authentication failures, token reuse in privileged sessions, and authentication paths where MFA enforcement doesn't match policy intent.
Govern NHI and Service Account Privilege Accumulation.
Service accounts and NHIs that bypass PAM accumulate privilege over time. AuthMind continuously maps their access, detects over-privilege relative to actual usage, and identifies accounts holding more access than their operational role requires.

Why it matters
Privileged access governance cannot end at the PAM boundary.
The identities operating outside that boundary, NHIs, bypassed workflows, and unmanaged admin paths, represent the highest-risk gaps in your access control posture. AuthMind closes them.









