
USE CASES
Advanced Identity Threat Detection & Response
Stop the attacks that already got past your controls.
Summary
Attackers aren't only focused on exploiting unknown vulnerabilities. Now, they're logging in. By the time most organizations detect a breach, adversaries have been in the network for weeks. Existing tools enforce policy at provisioning and go silent the moment access is granted. That gap is where attacks live and move
Key Business Challenges
Identity attacks succeed where visibility ends.
Adversaries weaponize legitimate credentials, exploit federation trust chains, and operate entirely within approved access paths. Insiders exploit the same gaps. Whether the threat originates outside the organization or from within, the attack surface is the same: valid identities doing things they shouldn't, across endpoints, network, SaaS, cloud, and IdP activity that most organizations cannot see.

Identity Perimeter Exposure
Endpoints, network, SaaS, cloud, and IdP activity form the identity perimeter. Most organizations have no unified visibility across it, leaving attackers free to move undetected.

Authentication Abuse & MFA Bypass
Adversaries bypass MFA through push fatigue, adversary-in-the-middle proxies, and helpdesk social engineering, arriving inside your environment with a valid, uncontested session.

Insider Threats Hidden in Plain Sight
Privilege abuse, living-off-the-land lateral movement, and unauthorized credential sharing happen entirely inside approved access paths, invisible to tools that only know what access is supposed to look like.

Fragmented, Context-Free Detection
SIEM generates noise. EDR misses identity plane movement. IAM tools go silent after provisioning. No single tool sees the full access chain, and attackers exploit every seam.
How AuthMind Solves These Challenges


Identity observability-driven threat detection and response.
AuthMind is the only ITDR solution that detects threats by observing the full identity access chain across human, NHI, and agentic AI identities, not just the login event. Patented AI and ML Identity Access Flow Graph technology continuously correlates identity activity, network flows, and cloud telemetry, delivering real-time context into who accessed or authenticated, from where, to what system, assuming which role, and whether any of it breaks pattern.
Where a conventional tool sees a successful login, AuthMind sees the full access path chain from the external to the internal, connecting both and any threat they represent.
Detect Advanced External Threats
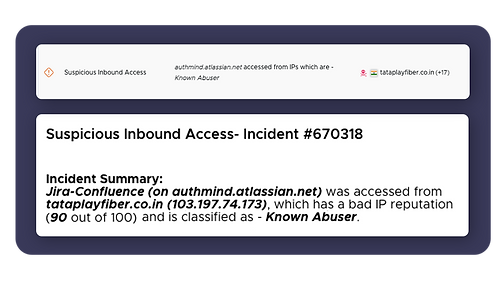
Detects MFA bypass, IdP compromise, token theft, and suspicious access patterns across every external attack vector in real time.

Detect Insider Threats with Precision
Detects AD attacks, privilege abuse, lateral movement such as LOTL, and credential misuse, including threats that bypass PAM and hide inside legitimate access paths.
Accelerate Detection and Response
Automates containment and delivers full identity context across human, NHI, and agentic AI identities to SOC, compressing investigation and response from hours to minutes.

Why it matters
By continuously observing what every identity actually does after authentication, AuthMind detects the attacks that passed your controls and stops them before they become breaches.
Most tools manage what identities are supposed to do. AuthMind protects organizations from what identities, including AI agents, NHIs, and human users, actually do. That is the difference between governance and security.









