
SOLUTION
Advanced Identity Threat Detection & Response
Attackers are using AI to move faster. Your identity detection and protection needs to keep up.
Summary
Attackers aren't only focused on exploiting unknown vulnerabilities. Now, they're logging in, and increasingly, they’re using AI to do it faster, at greater scale, and with greater precision than any manual investigation can identify.
By the time most organizations detect a breach, adversaries have been in the network for weeks. Existing tools enforce policy at provisioning and go silent the moment access is granted. That gap is where attacks live and move

Key Business Challenges
Identity attacks are evolving faster than your tools
Identity attacks come from two directions simultaneously, and increasingly, they converge. External adversaries use AI to accelerate credential attacks and find exploitable paths. Insiders abuse the same infrastructure from within. The attack surface is similar: valid identities, moving through approved access paths, doing things they shouldn't but undetected by current tools.

EXTERNAL THREATS
What AI-powered
attackers are targeting.
Adversaries are using AI to automate credential attacks, bypass MFA, and identify high-value access paths faster than traditional detection can respond. By the time most tools surface a signal, the attacker has already authenticated, moved, and established persistence.
-
MFA bypass via push fatigue, adversary-in-the-middle proxies, or SIM swapping
-
IdP compromise and federation trust chain abuse
-
Token theft and session hijacking after a successful authentication
-
Credential stuffing and password spray against Active Directory and cloud directories
-
Helpdesk social engineering to reset MFA and hijack accounts
-
Supply chain identity compromise through third-party integrations

INSIDER THREATS
The threat that's
already inside.
Insiders, whether malicious or compromised, exploit the same access paths as external attackers, but they're already authenticated. Living-off-the-land techniques make their activity nearly indistinguishable from legitimate IT operations without full identity access chain visibility.
-
Privilege abuse and lateral movement using native admin tools to avoid detection (living-off-the-land)
-
Unauthorized credential sharing and access token delegation
-
Data exfiltration through fully authorized, policy-compliant access paths
-
Shadow access to unmonitored assets and systems outside IAM governance
-
Departing employees retaining active access post-termination
Whether the threat originates outside the organization or within it, the attack surface is the same and the tools most organizations rely on were never built to see it. AuthMind observes and automatically remediates both, simultaneously, across the full identity perimeter.
How AuthMind Solves These Challenges


You can only fight AI-driven identity attacks with an AI-driven advanced ITDR defense.
AuthMind is the only Identity and security solution that continuously tracks identity access and activity across the full identity perimeter, correlating activity across agentic ai, NHI and human identities in real time. Patented AI and ML Identity Access Flow Graph technology observes every access path, detects behavioral deviations the moment they occur and automates response before potential damage is done, across every attack channel, internal or external, simultaneously.Where a conventional tool sees a successful login, AuthMind sees the full access path chain and flags when that chain breaks pattern, even when every individual action appears legitimate.
Detect Advanced External Threats
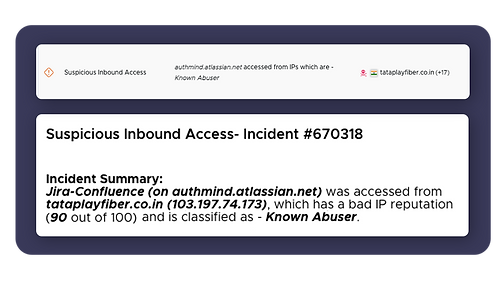
Detects MFA bypass, IdP compromise, token theft, impossible travel and suspicious access patterns across every external attack vector in real time.

Detect Insider Threats with Precision
Detects AD attacks, privilege abuse, lateral movement such as LOTL, and credential misuse, including threats that bypass PAM and hide inside legitimate access paths.
Discover Posture Blind Spots
Shadow assets, missing MFA, dormant service accounts, and users circumventing controls surfaced and remediated automatically, before attackers can exploit them.


Accelerate Detection and Response
Automates containment and delivers full identity context across human, NHI, and agentic AI identities to SOC, compressing investigation and response from hours to minutes.
Why it matters
By continuously observing what every identity actually does after authentication, AuthMind detects the attacks that passed your controls and stops them before they become breaches.
Most tools manage what identities are supposed to do. AuthMind protects organizations from what identities, including AI agents, NHIs, and human users, actually do. That is the difference between governance and security.









