Suspicious Identity Access: Early Indicators of Token-Based Threats detected by AuthMind
- AuthMind Team
- Nov 18, 2025
- 5 min read

In August 2025, attackers exploited stolen OAuth tokens tied to the Salesloft Drift integration to gain unauthorized access to multiple Salesforce environments. This wasn’t a flaw in Salesforce; rather, it was a breach of trust. By hijacking the tokens of a trusted app, the attackers were able to move freely through customer instances, extracting data and expanding their attack surface before anyone realized something was amiss.
What made this attack particularly alarming was its scale. It affected not only smaller companies but also large, security-mature organizations. Major players like Salesforce, Google, Palo Alto Networks, and Zscaler were forced to revoke integrations, reset tokens, and conduct internal investigations. For days, companies scrambled to understand what had been accessed, what data had left their environments, and how a seemingly routine integration could lead to
such widespread exposure.
Google’s own threat intelligence team later confirmed that some Google Workspace accounts connected through Drift were accessed using stolen tokens. Salesforce had to disable the integration entirely, revoking every active Drift token across tenants. This was a chain reaction through the SaaS ecosystem, one integration’s compromise rippling across platforms and customers globally.
The incident served as a blunt reminder that token-based trust can be just as fragile as password-based trust, and far harder to monitor.
The Systemic Gaps that Enable Token Attacks
Despite years of progress in SaaS security, token-based attacks persist for several
interconnected reasons:
1. Expanding SaaS ecosystems
Modern enterprises run hundreds of interconnected SaaS apps. Every new connection from chatbots to marketing tools introduces another trust relationship. Each integration carries its own OAuth tokens or SAML assertions, multiplying potential exposure points.
2. Over-permissioned and long-lived tokens
Developers often grant “all-access” scopes for convenience and productivity. Once issued, these tokens may stay valid for months, even years. Attackers know this and actively target integrations where tokens rarely expire or rotate.
3. Limited visibility into delegated access
Traditional security monitoring tools are built around endpoints and users, not app-to-app communication. OAuth traffic flows behind the scenes, inside APIs, and rarely surfaces in SIEM dashboards unless explicitly tracked.
4. Incomplete identity hygiene
Many organizations don’t maintain centralized inventories of which tokens exist, who issued them, and what scopes they cover. When a vendor discloses a breach, teams scramble to find out whether their environment was even connected.
5. Human and process gaps
Even the best technology can’t help if token governance isn’t prioritized. Security teams may overlook integrations that seem low risk, assuming vendors handle protection. Attackers exploit exactly that assumption.
This is why token abuse isn’t going away; it thrives in the shadows between convenience and oversight.
The Silent Risk Inside Trusted Integrations
OAuth and SAML were designed to make authentication seamless. Instead of requiring repeated logins, they allow applications to “delegate” access to act on behalf of a user or another service. It’s efficient, but that convenience hides risk.
Once a token is granted, it can remain valid for long periods unless deliberately revoked. Many apps ask for excessive permissions, and once compromised, those same permissions become an attacker’s toolkit. Unlike a password theft, token misuse often doesn’t trigger MFA challenges or login alerts.
The real danger lies in how quiet these attacks can be. The traffic looks legitimate. The access appears expected. Tokens don’t break anything; they just bend trust until it snaps.
By the time anomalies are obvious, such as large data exports or activity from foreign IP addresses, the breach has often been underway for days or weeks.
Reading the Identity Signals: Patterns that Stood Out
While the Salesloft Drift breach was unfolding, AuthMind analyzed telemetry across several customer environments. Even for organizations that weren’t directly using the compromised integration, certain behaviors stood out. These were identity-centric clues, subtle signals of possible compromise that often precede major incidents.
NHI-like Behavior by Users
AuthMind observed periodic, automated sequences of activity from some user identities. Instead of random human logins or ad hoc actions, these accounts showed consistent, clocklike intervals, the kind of behavior associated with nonhuman interaction or scripted processes.These repetitive patterns diverged from each user’s historical baseline and triggered an investigation.

Spike in User Access
In multiple environments, specific identities exhibited sudden, sharp increases in access volume. These spikes appeared on isolated days, far above what the same users typically generated. Even when no direct link to Drift existed, these anomalies suggested credential or token misuse, a red flag for any security team.
Suspicious Inbound Access from Malicious IPs with High Risk
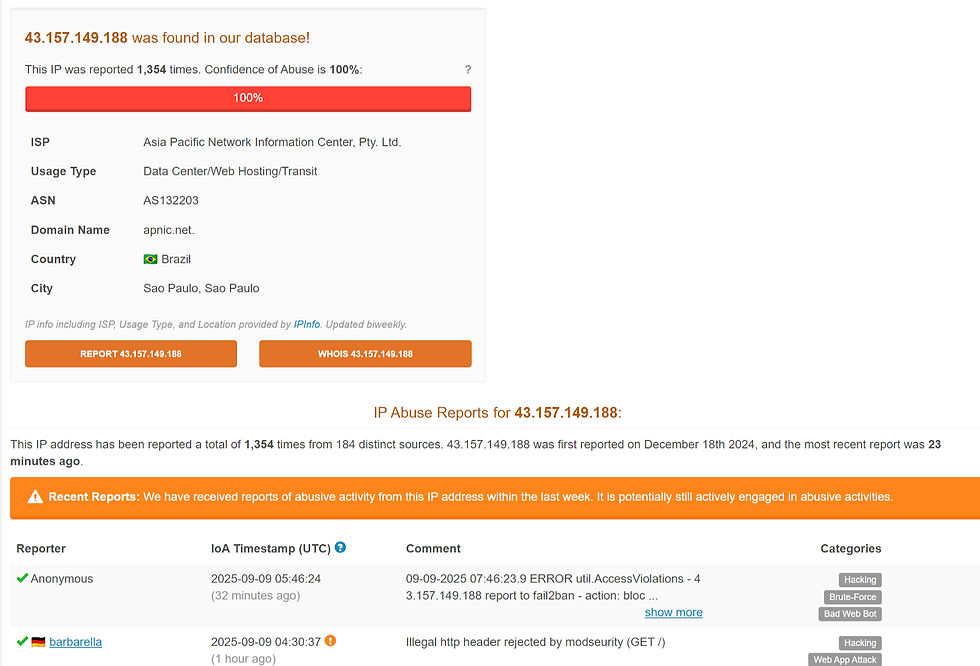
AuthMind also detected inbound access from IP addresses that were later classified by reputation databases as malicious or high-risk. Some of these addresses were previously unseen within those organizations, making them immediate outliers. Correlating this data with identity activity provided early warning of potential exploitation paths.

These findings underscored a key point: you don’t need to be the target of a specific breach to detect its side effects. When you watch how identities behave, patterns reveal themselves.
Turning Identity Signals into Early Defense
Faster Awareness, Smaller Impact
Organizations that rely solely on reactive vendor notifications often learn of breaches days after they begin. Behavioral anomalies spike, new IP sources, and automation-like behavior surface faster. That visibility can narrow the breach window from days to hours.
Stronger Defensive Posture
When you identify deviations early, you don’t just react, you proactively contain. Isolate the user, revoke the token, or rotate keys before the attacker has time to escalate privileges or exfiltrate more data.
Better Investigation Context
Each alert in AuthMind carries full context: which and what type of identity was involved, what actions deviated from baseline, where the traffic originated, and whether the IP has external risk signals. That clarity cuts investigation time and helps defenders focus on the few events that truly matter.
A Proactive Security Mindset
The Salesloft Drift attack highlights a simple truth: trust is now an attack surface. Modern defense isn’t only about patching vulnerabilities or blocking malware. It’s about watching how identities act because abnormal identity behavior is often the first sign of compromise.
The Takeaway
Even the most reputable SaaS platforms can’t fully protect customers from the misuse of integrations. OAuth and SAML tokens are convenient, but they also blur the line between legitimate automation and malicious access. Once an attacker gains a valid token, traditional perimeter controls are powerless.
That’s why identity observability is essential. By tracking every access, organizations are able to have full visibility into how identities behave when, how often, from where, and at what scale, allowing them to uncover the small signals that reveal big threats.
Unusual behavior isn’t just noise; it’s early evidence. It’s the opportunity to respond before data leaves your environment.
When identity behavior shifts in timing, volume, source, or method, it’s not just a deviation; it’s a warning. Recognizing that shift early changes the story from damage control to prevention. AuthMind makes that awareness possible.










Comments